Messari has released a comprehensive report examining Forta's approach to addressing cryptocurrency's security challenges. Key highlights:
- Forta Firewall uses neural networks for real-time threat analysis
- System provides ultra-low latency transaction monitoring
- $FORT token utility continues to expand
- Platform aims to enable secure, compliant blockchain operations
The report details how Forta's technology could help scale crypto adoption through enhanced security measures. Their AI-powered system analyzes transactions before they reach the blockchain, offering preventative protection rather than reactive solutions.
Learn more: Messari Report
If crypto isn't safe, it won't scale. @MessariCrypto published a full report on Forta, framing crypto’s security problem and how Forta Firewall is built to solve it with real-time threat prevention and growing $FORT utility. Forta is building a secure and compliant onchain
Forta Network is redefining onchain security. Our latest report explores how its Firewall uses AI to block malicious activity before execution—already integrated with Mode, Plume, and Balmy, and analyzing nearly 200K txs/day. Full breakdown: messari.co/4jB4wle
Custom-built for crypto, Forta Firewall’s neural network analyzes live transactions with ultra-low latency to stop threats before they hit the chain. Here’s how it works 👇
The @MessariCrypto report on Forta highlights how it’s positioned to solve one of crypto’s most pressing problems: security. With real-time threat prevention and growing $FORT utility, Forta is helping build a safer onchain economy. Check the report: messari.io/report/underst…
🚨 Missing Access Control Drains $257.8K from Ethereum Protocol
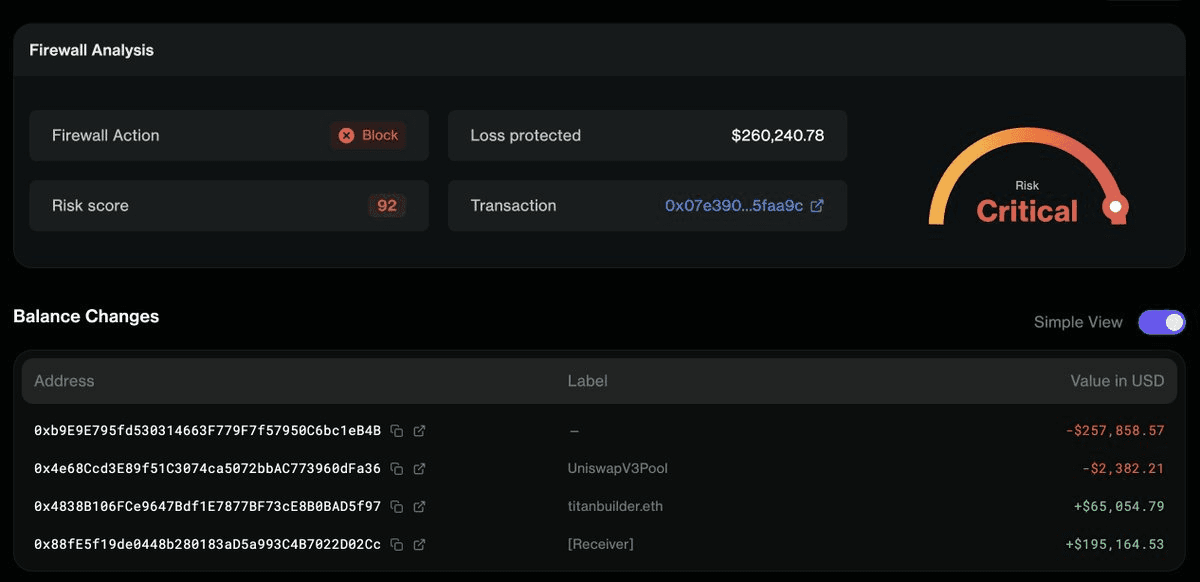
A vulnerability in a Uniswap V3 callback function led to a **$257.8K exploit** on Ethereum. The attack exploited a **missing access control check** on the `uniswapV3SwapCallback` function, allowing unauthorized execution. **Key Details:** - Attack vector: Unprotected callback function in smart contract - Amount lost: $257,800 - Network: Ethereum mainnet - Detection: Flagged by real-time security monitoring **Technical Context:** The vulnerability highlights a common smart contract security gap where callback functions lack proper access restrictions. Without validation that only authorized contracts can trigger callbacks, attackers can manipulate execution flow. This incident follows recent price manipulation exploits on Ethereum and BSC, where attackers used flash loans and unprotected swap functions to drain liquidity pools. **Prevention Measures:** - Implement access control checks on all callback functions - Use slippage protection in swap operations - Deploy pre-execution security screening - Audit contracts before deployment Real-time detection systems caught the exploit as it occurred, demonstrating the value of continuous blockchain monitoring for identifying attack patterns before significant damage occurs.
NEAR Protocol Loses $7M to Fake Token Attack
**NEAR Protocol suffered a $7 million loss** due to fake tokens, highlighting critical gaps in blockchain security infrastructure. The incident underscores a broader trend: **$92M was lost to crypto exploits in March alone** across 33 separate incidents. **Key takeaway:** Real-time on-chain monitoring is no longer optional for blockchain projects and institutions. Transaction screening must be implemented as a fundamental security layer, not an afterthought. This attack demonstrates why proactive security measures are essential as more institutions move on-chain.
Polkadot Bridge Exploited: Infinite Minting Drains $237K
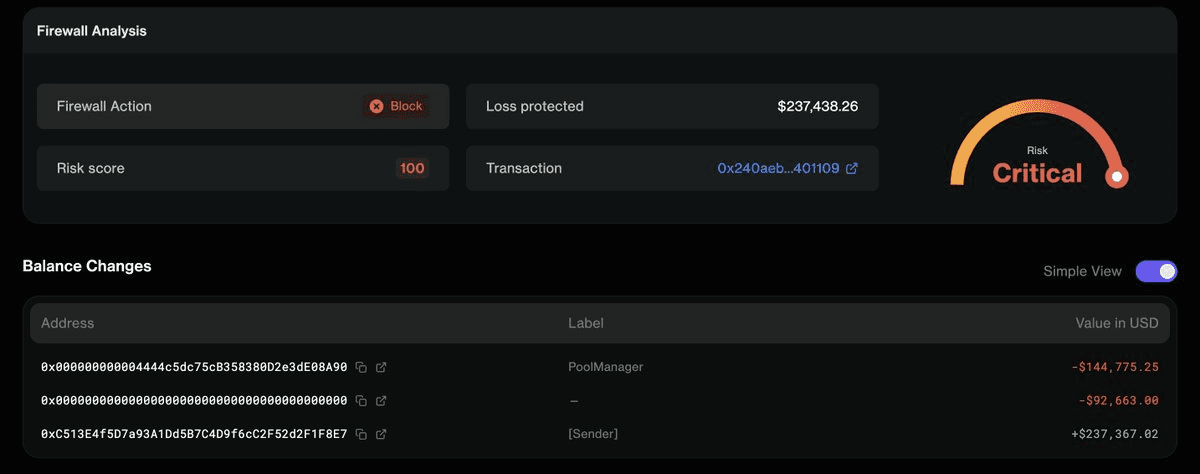
A critical security breach on the Polkadot bridge allowed an attacker to gain admin access and mint unlimited bridged DOT tokens. **What happened:** - Forged cross-chain message bypassed state proof validation - Attacker gained admin control over bridged DOT token contract - Infinite minting enabled, entire supply dumped for $237,000 - DOT price crashed to near zero Forta Firewall detected and flagged the exploit in real-time, but the damage was already done. **The bigger question:** This incident highlights the ongoing vulnerability of cross-chain bridges and raises concerns about whether DeFi protocols are taking security infrastructure seriously enough.
IoTeX Bridge Loses $8M in 90 Minutes Through Compromised Private Key
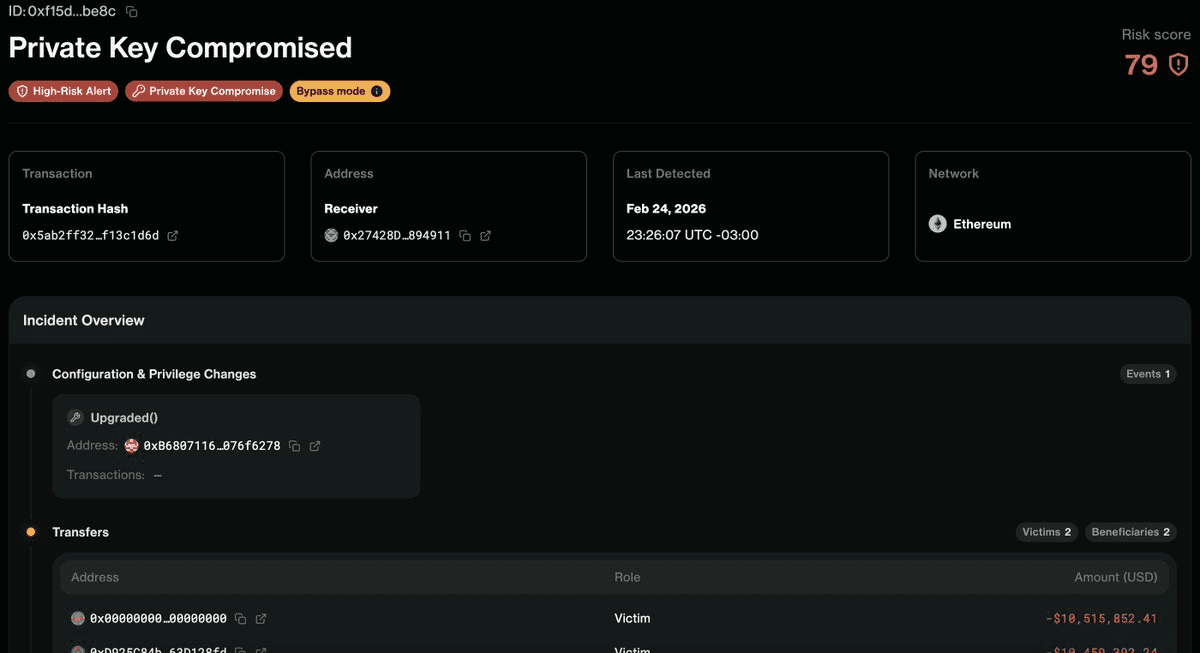
**IoTeX Bridge Exploit: $8M Drained** The @iotex_io Bridge suffered a major security breach on February 28, 2026, losing $4.3M initially and escalating to $8M within 90 minutes. The attack was executed through a single compromised private key. **Key Details:** - Attack vector: Compromised private key - Timeline: $4.3M → $8M in 90 minutes - Detection: Forta Firewall caught the attacker's mainnet movements in real-time **Recent Context:** Just two days earlier, a @FOOMCASH lottery-contract exploit put $1.8M at risk. Forta Firewall flagged the attack in real-time and successfully blocked it on Firewall-enabled chains. This incident highlights the ongoing security challenges in cross-chain infrastructure and the critical importance of private key management in blockchain systems. Real-time detection systems like Forta Firewall are proving essential for identifying threats, though prevention remains dependent on proper security practices. Learn more about Forta Firewall: [Introducing Forta Firewall](https://forta.org/blog/introducing-forta-firewall/)
Forta Firewall Featured in Messari's State of AI Report
**AI-powered blockchain security gains recognition** as Forta Firewall appears in Messari's latest State of AI report. The inclusion highlights how **artificial intelligence is becoming integral** to onchain security infrastructure. Forta's AI-driven transaction screening technology represents the evolution of blockchain defense mechanisms. - AI-powered attackers require AI-powered defenders - Real-time transaction screening at scale - Growing integration across multiple blockchain networks With **290M+ transactions already screened**, Forta Firewall demonstrates practical AI implementation in blockchain security, moving beyond theoretical applications to active threat detection.
