This article provides guidelines for writing effective vulnerability reports. It emphasizes the importance of clearly highlighting the vulnerability, providing a detailed breakdown, explaining the potential impact, including a coded Proof of Concept (POC), and offering straightforward mitigation recommendations. Following these guidelines may increase the chances of the report being labeled as 'selected for report' and potentially increase rewards.
Did you know that issues labeled as "selected for report" can potentially increase your rewards? Naturally, you’re probably now thinking “how can I get my finding labeled as such? What makes a good write-up?” Lucky for you, we’re going to showcase a good example of just that.
Monetrix Audit Report Published After $22,000 Competition
Code4rena has released the complete audit report for Monetrix following a competitive security review. **Key Details:** - The audit competition awarded $22,000 in prizes to security researchers - ABAIKUNANBAEV secured their first-ever 1st place finish in the competition - Multiple valid security findings were submitted and addressed - The Monetrix team demonstrated commitment to security standards throughout the process The full audit report is now available for review at [code4rena.com/reports/2026-04-monetrix](https://code4rena.com/reports/2026-04-monetrix). This follows Code4rena's recent publication of the Olas audit report, continuing their track record of transparent security reviews in the Web3 space.
Olas Security Audit Report Published by Code4rena
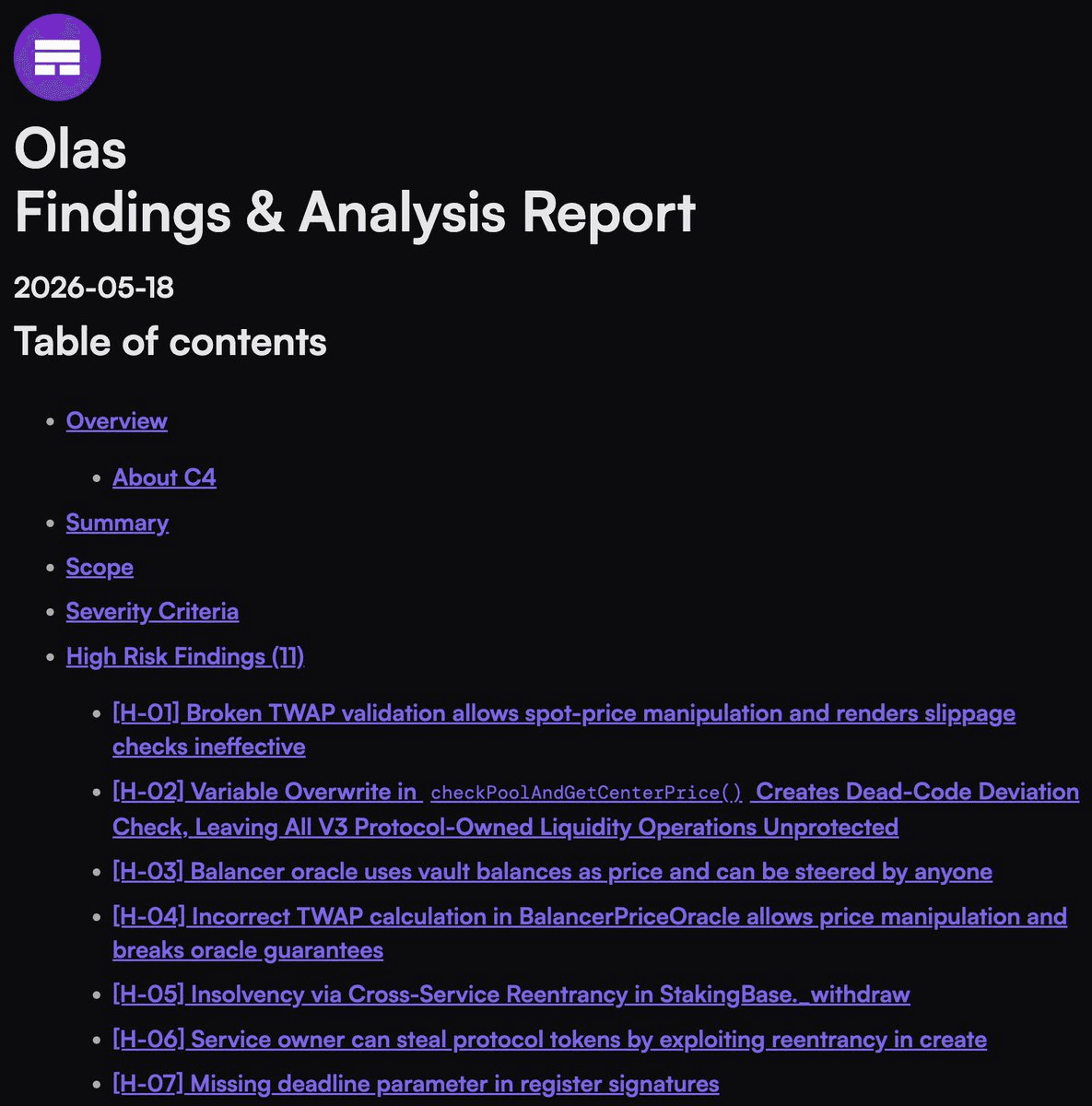
The Olas protocol has released its latest security audit report through Code4rena, a competitive smart contract auditing platform. **Key Points:** - Audit report now publicly available at [code4rena.com/reports/2026-01-olas](https://code4rena.com/reports/2026-01-olas) - Demonstrates Olas team's commitment to security standards - Code4rena uses competitive auditing to identify vulnerabilities faster than traditional methods The audit represents another step in Olas's ongoing security practices, with the team maintaining transparency through public disclosure of findings.
🔍 K2 Lending Protocol Launches 40-Day Security Audit Competition on Code4rena
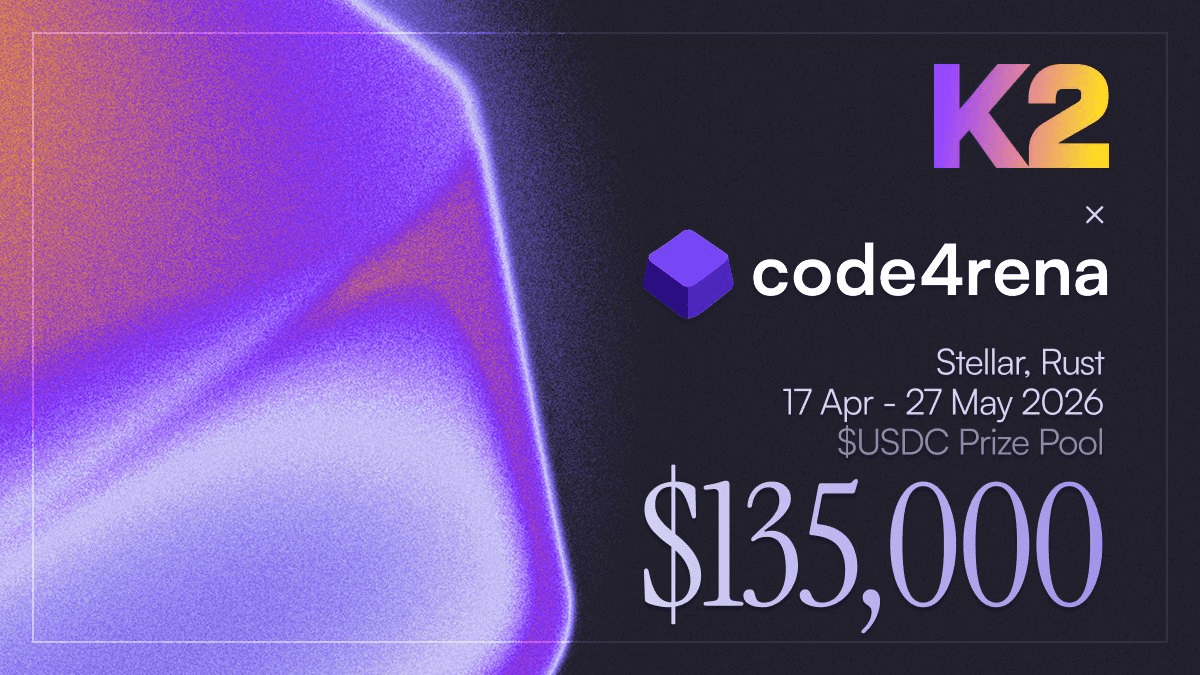
**K2 Lend**, a new lending protocol on Stellar, has launched a competitive security audit on Code4rena running for 40 days. **Key Details:** - Features pooled, isolated, and gated lending markets - Largest prizes awarded for most unique and severe vulnerabilities discovered - Security researchers can access [audit documentation](https://code4rena.com/audits/2026-04-k2) to begin analysis The competitive audit format allows multiple security researchers to simultaneously review the protocol's smart contracts, with compensation based on the severity and uniqueness of bugs found.
Intuition Launches $100,000 Bug Bounty on Code4rena
**Intuition has launched a major bug bounty program** on Code4rena with a **$100,000 reward pool** for security researchers. The bounty targets whitehats to identify valid vulnerabilities in Intuition's smart contracts. Participants can: - Review detailed bounty specifications - Explore publicly known issues - Check the contest scope and requirements This represents a significant investment in security auditing through Code4rena's competitive platform. **Ready to hunt for bugs?** [Check out the full bounty details](https://code4rena.com/bounties/intuition)
Panoptic Returns to Code4rena for Another Competitive Security Audit

**Panoptic is launching another competitive audit** with Code4rena to secure their Next Core codebase. This marks **multiple successful collaborations** between the two platforms, building on previous audit rounds that helped strengthen Panoptic's security posture. Key details: - Focus on **Next Core codebase** security - Competitive audit format with community participation - Part of ongoing security partnership The audit represents Panoptic's continued commitment to thorough security practices as they develop their DeFi infrastructure.