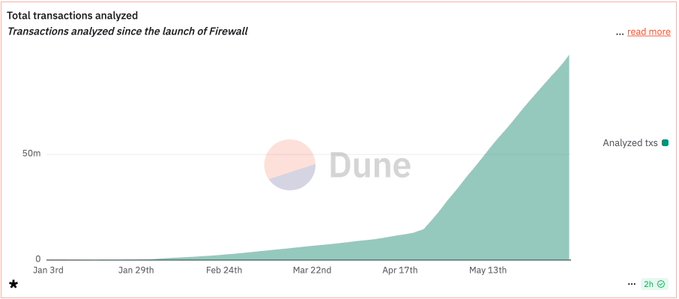
Forta Firewall Scales to 25M Transactions in 10 Days
Forta Firewall Scales to 25M Transactions in 10 Days
🔥 25M Tx Later...

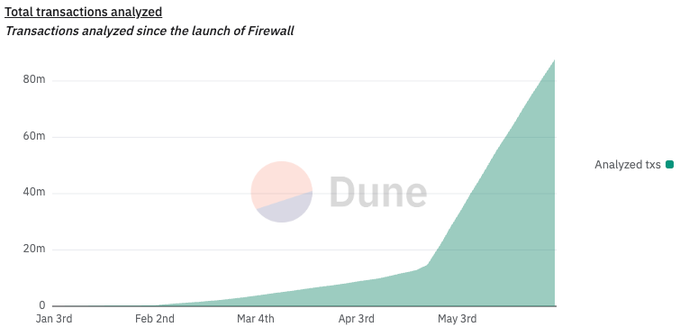
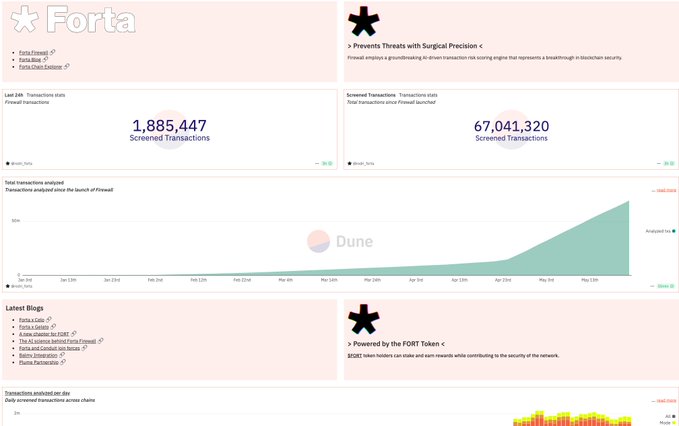
Forta Firewall continues its rapid expansion across multiple blockchain networks, screening 25 million transactions in just 10 days. The security protocol has demonstrated significant growth since May 2025:
- Now screens over 2M transactions daily
- Protects major networks including Celo, Mode, and Plume
- Reached 150M+ total screened transactions
- Secures 180+ apps with $4B in assets
The AI-powered system evaluates every transaction for threats before they reach the chain, providing real-time security and compliance for rollups.
Track live metrics: Forta Firewall Dune Dashboard
Over the weekend, Forta Firewall screened 3.6M+ transactions across rollups 📈 With adoption growing fast, Firewall scales effortlessly, keeping rollups secure and compliant with real-time threat prevention 🛡️ Built for scale. Powered by AI.
More than 12 million transactions screened on @plumenetwork, and not a single one made it through without passing Forta Firewall. Real-time protection, built into the chain. Security by default.
Forta Firewall is LIVE on @Celo and already screening every transaction in real time. Millions processed so far. Every tx evaluated before it hits the chain 🔗 Security is no longer optional, it’s built in 🛡️
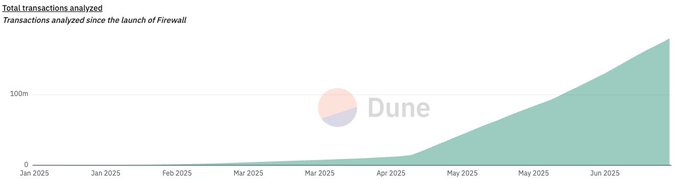
Forta Firewall crossed 150 MILLION screened transactions over the weekend. Adoption is accelerating across rollups. On-chain protection, at scale.
Over 25M transactions screened in just 10 days 🚀 Forta Firewall is scaling, and scaling fast. Track the metrics on the Forta Firewall Dune Dashboard: dune.com/forta_team/for…
Forta Firewall has already scanned 70M+ transactions on @Celo. Every single one evaluated for potential threats before hitting the chain. That’s what security by default looks like.
Forta Firewall is available to every rollup building with @gelatonetwork 🛠️ Real-time exploit & compliance screening, no custom setup needed. Security + compliance, built-in.
What AWS is to Web2, Gelato is to Web3. Infra that powers rollups, wallets, and apps—at scale. From chain deployment to RPCs to Account Abstraction. One platform. All of Web3.
Forta Firewall is now live on @Celo 🔥 Every transaction screened. Every attacker stopped. Every user protected. Security by default.
Forta Firewall is scaling fast 📈 67M+ transactions already screened and growing daily. Powered by the $FORT token, securing chains in real time. Check the metrics on the new Dune dashboard: dune.com/forta_team/for…
Between @Celo, @modenetwork, @plumenetwork, and a few others we can’t name just yet 👀, Forta Firewall is now screening over 2 million transactions daily Ethereum L2s are scaling, and Forta Firewall is making sure they stay secure and compliant.
180+ apps. $4B in assets. @plumenetwork didn’t just launch, they armed up 🛡️ Forta Firewall screens every single transaction on Plume before it hits the chain. Learn more -> forta.org/blog/forta-fir…
And just like that… 100 million transactions screened by Forta Firewall 🚀 Real-time security and compliance for rollups, blocking threats before they hit the chain. Prevention is the new standard 🛡️
Forta Firewall 🤝 @plumenetwork On Day 1 of Plume mainnet, we’re proud to protect protocols with real-time, AI-powered transaction screening, stopping malicious activity before it hits the chain. Built for a permissionless and composable RWAfi future. The future is secure 🪶
Forta Firewall is now screening more than 2 million transactions every day, before they hit the chain. Real-time protection at scale. And growing fast.
In case you missed it 👀 Catch up on the latest from Forta 🧵👇
More than 70 MILLION transactions have now been screened by Forta Firewall 🛡️ Powered by $FORT. Securing chains in real time. Without security, the onchain economy can’t grow. Forta is making sure it does.
SquidMulticall Loses $517K in Cross-Chain Exploit via Stale Token Approvals
**Attack Overview** SquidMulticall suffered a $517K loss when an attacker exploited pre-existing MAX_UINT token approvals. The exploit affected multiple chains including Arbitrum, BSC, Avalanche, Optimism, and Base. **How It Happened** - Victims had previously granted unlimited (MAX_UINT) token approvals to the SquidMulticall contract - The attacker leveraged a permissionless multicall function to drain funds - No traditional "hack" was needed - users had already signed away access to their tokens **Key Takeaway** Stale token approvals represent a silent but significant attack surface. Old unlimited approvals can be exploited even if the original contract or protocol is no longer actively used. Forta Firewall detected the suspicious activity across all five affected chains. **Action Item**: Review and revoke unnecessary token approvals regularly using tools like Revoke.cash or Etherscan's approval checker.
Wasabi Protocol Loses $5.5M in Admin Key Compromise Attack
**Wasabi Protocol suffered a $5.5M exploit** after a compromised deployer granted admin roles to malicious contracts, leading to a complete drainage of the protocol. **Key Details:** - The attacker exploited compromised admin credentials to drain 7 vaults - Affected chains included Base and Ethereum - A fake strategy contract was used to execute the theft - Forta Firewall had flagged the suspicious ADMIN_ROLE grant **Security Implications:** This incident highlights that operational security (OpSec) is just as critical as smart contract security. Even well-audited protocols remain vulnerable if admin keys are compromised. The attack demonstrates the ongoing need for robust key management practices and real-time monitoring systems in DeFi protocols.
April Sets Record with $320M in Crypto Exploits

April 2026 marked the worst month in crypto history with over $320 million drained across multiple exploits, including the $280 million Kelp incident. **Key Statistics:** - $320M+ lost in April alone - Follows $92M in losses across 33 incidents in March - Total of $412M+ drained in just two months **Security Response:** Forta's Firewall technology integrates directly into transaction flows to screen and block threats before execution. The system provides real-time transaction screening for chains and institutions moving onchain. The escalating exploit activity underscores the critical need for proactive security measures in blockchain infrastructure.
OFAC Sanctions Ethereum Addresses Tied to Sinaloa Cartel, Forta Firewall Responds
The U.S. Treasury's Office of Foreign Assets Control (OFAC) has sanctioned new Ethereum addresses connected to Sinaloa Cartel fentanyl trafficking operations. **Immediate Response:** - Forta Firewall updated its monitoring systems to track the sanctioned addresses - Transactions involving these wallets are now flagged before execution - The system provides real-time onchain compliance screening This follows a pattern of rapid response by Forta Firewall to OFAC sanctions. In March, the platform similarly updated its blocking list within hours when Treasury sanctioned 20 Ethereum wallets linked to terrorism and North Korea. [Learn more about Forta Firewall](https://forta.org/firewall?utm_source=twitter&utm_medium=social&utm_campaign=firewall-update&utm_content=ink-case-study)
IoTeX Bridge Loses $8M in 90 Minutes Through Compromised Private Key
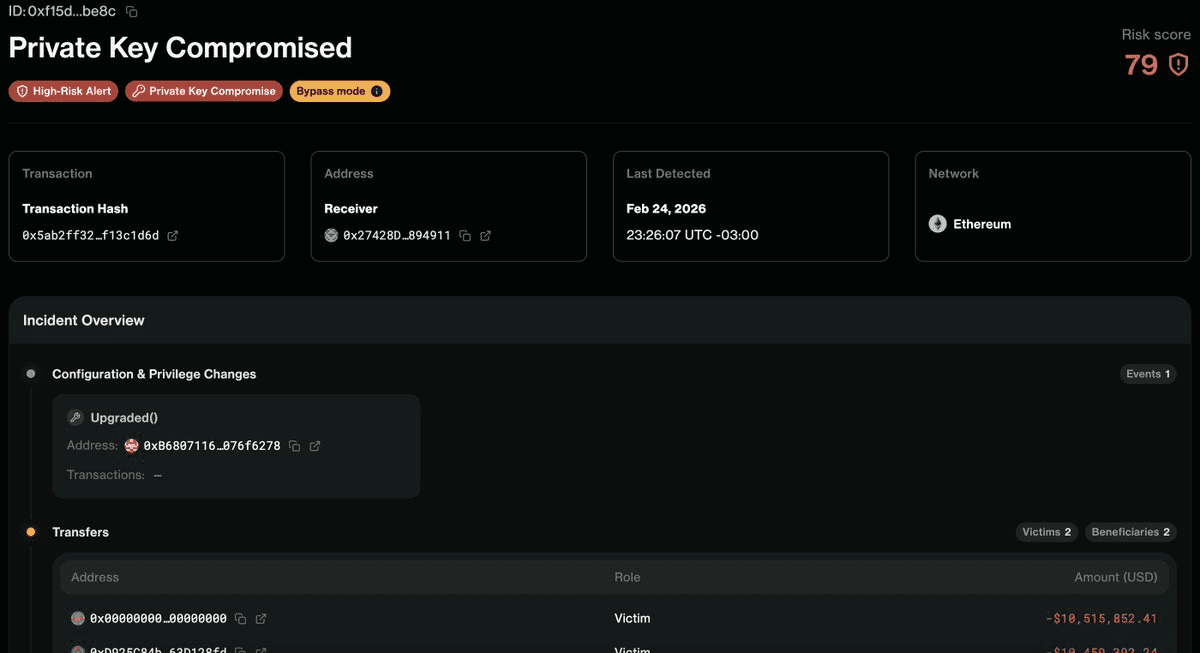
**IoTeX Bridge Exploit: $8M Drained** The @iotex_io Bridge suffered a major security breach on February 28, 2026, losing $4.3M initially and escalating to $8M within 90 minutes. The attack was executed through a single compromised private key. **Key Details:** - Attack vector: Compromised private key - Timeline: $4.3M → $8M in 90 minutes - Detection: Forta Firewall caught the attacker's mainnet movements in real-time **Recent Context:** Just two days earlier, a @FOOMCASH lottery-contract exploit put $1.8M at risk. Forta Firewall flagged the attack in real-time and successfully blocked it on Firewall-enabled chains. This incident highlights the ongoing security challenges in cross-chain infrastructure and the critical importance of private key management in blockchain systems. Real-time detection systems like Forta Firewall are proving essential for identifying threats, though prevention remains dependent on proper security practices. Learn more about Forta Firewall: [Introducing Forta Firewall](https://forta.org/blog/introducing-forta-firewall/)