Cryptocurrency has moved beyond digital screens into physical public spaces through art installations and sculptures.
An article on HackerNoon highlights five crypto-themed sculptures located in various locations worldwide that visitors can experience in person. These installations represent the intersection of blockchain technology and traditional art forms.
The pieces demonstrate how digital assets are being commemorated in tangible, physical formats - bringing abstract concepts like decentralization and cryptocurrency into our everyday environments.
These sculptures serve as conversation starters and educational tools, helping introduce broader audiences to crypto concepts through accessible art experiences.
Crypto is no longer just on your screen. Discover the surprising world of sculptures and art in public spaces worldwide that bring digital assets into our physical reality. Let’s explore! hackernoon.com/5-crypto-sculp…
Obyte Friends Incentivizes Network Growth Through New User Connections
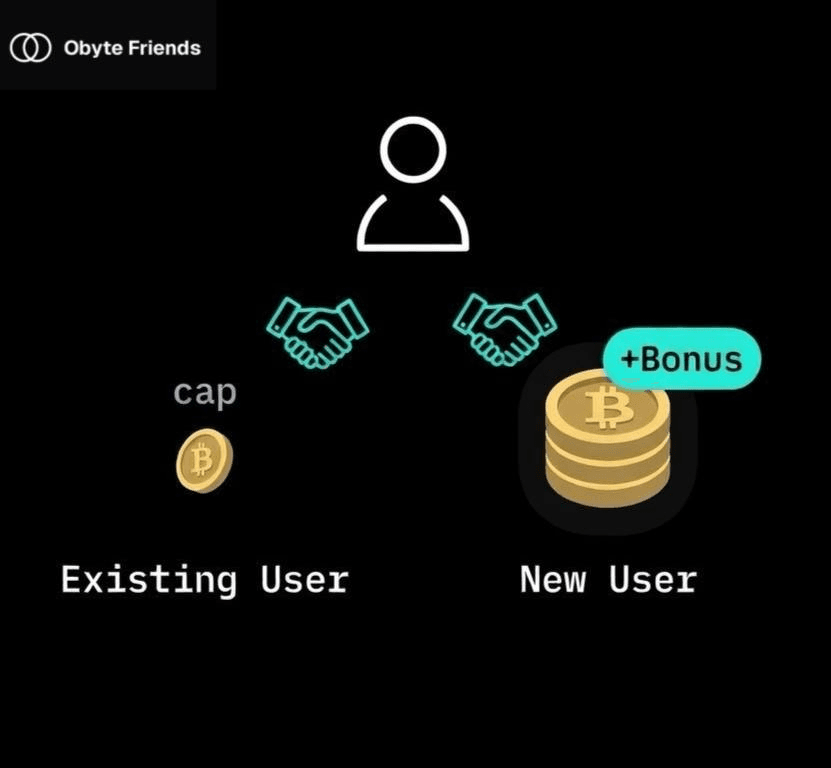
Obyte Friends introduces a tiered reward system that prioritizes bringing new users over connecting with existing ones. **Key differences:** - New user connections offer extra rewards with no balance cap - Existing user connections have limited reward potential - Follow-up rewards continue after initial connection, calculated on current balance **How it works:** Rewards split between locked and liquid FRD tokens. Locked balances compound at 1% over time, encouraging long-term participation. The structure aligns incentives toward network expansion rather than passive staking. Learn more at [Obyte Friends](https://friends.obyte.org)
The Real Horror Stories That Built Crypto and P2P Systems
A new analysis explores the **historical events** that drove the creation of cryptocurrency and peer-to-peer systems. The piece examines several key catalysts: - **Crypto Wars** - Government attempts to control encryption - **Fiat currency collapses** - Traditional money system failures - **eGold & Liberty Dollar** - Early digital currency shutdowns - **2008 Financial Crisis** - Banking system breakdown - **Censorship** - Information and financial restrictions These events demonstrate how **regulatory overreach** and **system failures** motivated developers to create decentralized alternatives. The article connects past financial disasters to present-day crypto adoption, showing how **freedom went digital** as a response to traditional system limitations. [Read the full analysis](https://hackernoon.com/real-horror-stories-that-urged-the-creation-of-crypto-and-p2p-systems)
Crypto's Centralization Problem: How Power is Concentrating Again
**Crypto's original promise of decentralization is under threat** as power slowly concentrates in the hands of major institutions and centralized entities. **Key centralization risks include:** - Large institutions like BlackRock entering the space - Traditional finance companies adopting crypto - Concentration of mining power and validator nodes - Centralized exchanges controlling significant trading volume **The challenge:** While crypto was built to eliminate middlemen, new forms of centralization are emerging that could undermine the core principles of financial freedom and permissionless access. **Potential solutions:** - Supporting truly decentralized protocols - Using non-custodial wallets and DEXs - Participating in governance of decentralized networks - Building and using platforms that prioritize decentralization The crypto community must remain vigilant to preserve the decentralized vision that sparked the blockchain revolution. [Read the full analysis](https://hackernoon.com/how-crypto-is-getting-centralized-and-what-we-can-do-about-it)
5 Steps to Recognize Legitimate Crypto Services
Protecting yourself in crypto requires due diligence. Here are key steps to verify legitimate services: - **Basic Signs**: Look for clear ownership, licensing, and regulatory compliance - **Documentation**: Review terms, policies, and legal frameworks - **Team Research**: Verify team members' backgrounds and credentials - **Security Measures**: Assess protection protocols and audit history - **Reputation Check**: Evaluate user feedback and transparency practices Read the detailed guide: [How to Recognize Legitimate Crypto Services](https://hackernoon.com/5-steps-to-recognize-a-legitimate-centralized-crypto-service#DeFi)