Ledger's CTO Charles Guillemet warns that AI is dramatically accelerating crypto security threats. Attack research that previously required months now completes in seconds, while expanding software creates more vulnerabilities.
Key Points:
- AI reduces exploit development costs toward zero
- Traditional post-breach patches are no longer sufficient
- Real-time, pre-execution threat prevention is now essential
The shift demands fundamental changes in how crypto systems approach security monitoring and defense.
"The cost is going down to zero" @Ledger CTO on AI-powered exploits 👀 More software, more attack surface. Tasks that once took researchers months now take seconds. The only answer is real-time, pre-execution threat prevention. Not patches after the fact. 👇
Address Poisoning Scam Costs User $386K in Simple Copy-Paste Attack
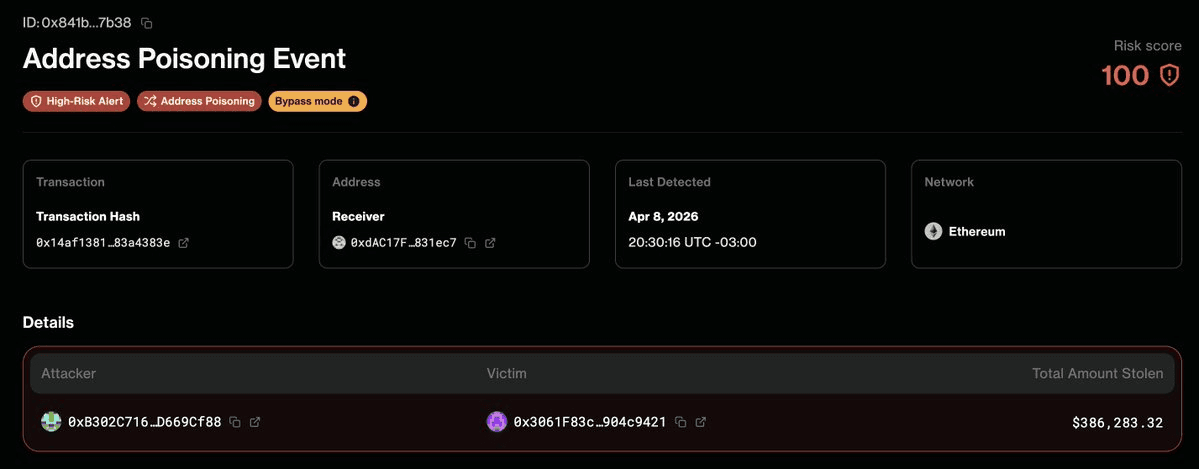
A user lost **$386,000** by sending funds to a fraudulent address that closely resembled a legitimate one in their transaction history. **How the attack works:** - Scammers plant near-identical addresses in a victim's transaction history - Users copying addresses from their history accidentally select the fake one - The attack exploits common habits rather than technical vulnerabilities This follows a similar **$600K USDT** address poisoning attack in February, where a look-alike address was planted 32 minutes before the victim's transaction. [Forta Firewall](https://forta.org/firewall?utm_source=twitter&utm_medium=social&utm_campaign=firewall-update&utm_content=ink-case-study) detected both incidents in real-time and can block such attacks on protected chains. **Protect yourself:** Always verify the complete address before sending transactions, not just the first and last few characters.
💸 Oops! $517K Drained Across 5 Chains Due to Token Approvals
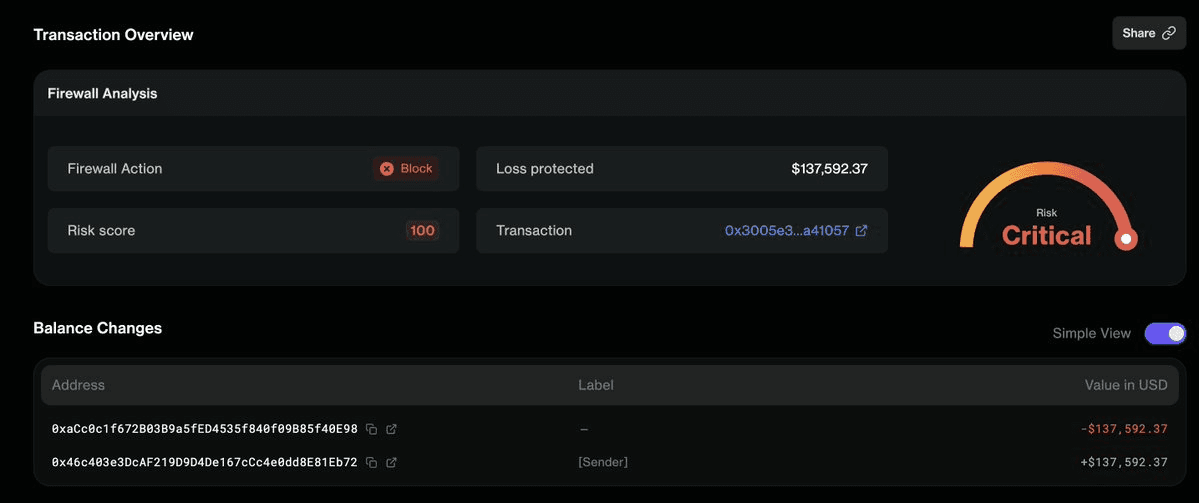
**A $517K exploit hit multiple chains** - Arbitrum, BSC, Avalanche, Optimism, and Base - without any traditional hack. **The vulnerability:** Users had previously granted MAX_UINT token approvals, which attackers exploited through a permissionless multicall function. This allowed draining of funds across all five chains simultaneously. **Detection:** Forta Firewall caught the suspicious activity across all affected networks. **Key takeaway:** Token approvals represent a significant attack surface. When you approve a contract to spend your tokens with unlimited permissions (MAX_UINT), those approvals remain active indefinitely - creating ongoing risk even from contracts you no longer use. This follows a similar pattern to January's $13.3M USDC drain on Base, where existing max approvals were exploited via an arbitrary-call vulnerability. **Action item:** Review and revoke unnecessary token approvals regularly to minimize your exposure.
Denaria Finance Loses $165K in Smart Contract Attack on Linea
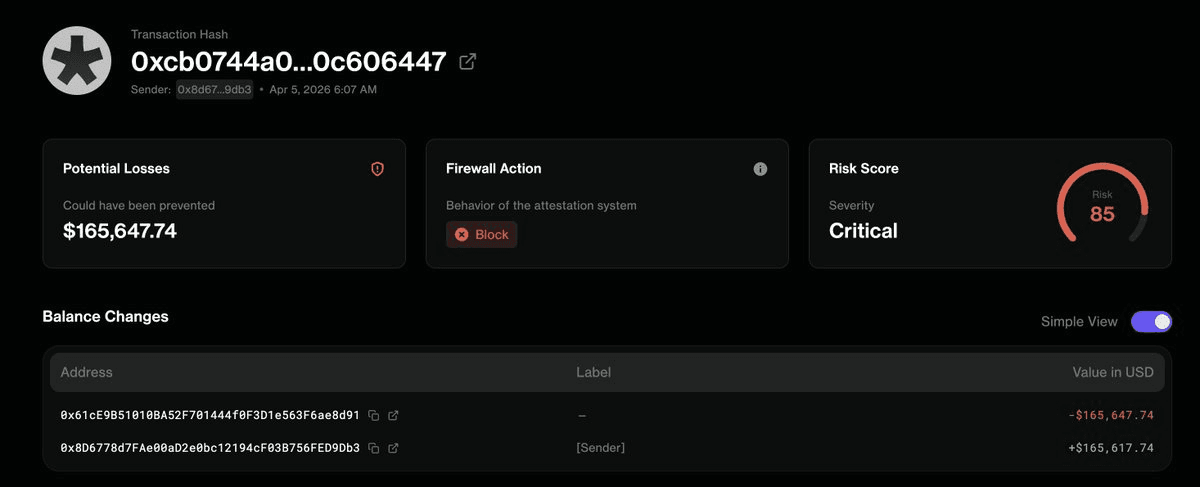
**Denaria Finance**, a perpetual trading platform on Linea, suffered a smart contract exploit resulting in approximately **$165,000 in losses**. The platform's interfaces are currently down as the team investigates the incident. **Key Details:** - Attack vector: Smart contract vulnerability - Platform affected: Perpetual trading protocol on Linea - Detection: Forta Firewall identified the exploit **The Broader Context:** This incident follows a pattern of DeFi exploits detected by Forta's monitoring system, including: - Recent Cyrus Finance exploit - October attacks on $FIRE ($57K) and $AIZPT ($20K) via price oracle manipulation The recurring theme: **pre-execution screening and real-time threat detection** can flag vulnerabilities before funds are drained, though implementation remains inconsistent across protocols.
Forta and Elliptic Partner to Integrate Scam Detection into Institutional Compliance Workflows
Scam activity continues to be a major source of losses in crypto. To address this, **Forta and Elliptic are partnering** to integrate scam intelligence into institutional compliance and risk workflows. The collaboration aims to: - Provide high-signal scam detection data - Enable faster institutional response to threats - Strengthen compliance processes with real-time insights This integration allows institutions to access Forta's detection capabilities alongside Elliptic's risk intelligence, creating a more comprehensive approach to identifying and responding to scam activity. [Read the full announcement](<http://forta.org/blog/forta-x-elliptic-bringing-scam-signals-into-broader-risk-and-compliance?utm_source=twitter&utm_medium=social&utm_campaign=elliptic&utm_content=elliptic-partnership>)